Member-only story

The Certified Red Team Operator (CRTO) course is an offering from Zero-Point Security that aims to teach “the basic principles, tools, and techniques, that are synonymous with red teaming”, with the accompanying exam giving you a shiny new badge saying that I am good at pretending to be a real bad guy. I recently completed this course and, thankfully, passed the exam. In this article, I will be going over my thoughts on the course, exam, and Zero-Point Security as a security training provider. Let’s get stuck in!
The CRTO course begins by giving a brief overview of red team engagements, their purpose, and the considerations one must take when planning and executing this type of security test. This is a good overview for anyone new to the idea of red teaming and helps newcomers distinguish a red team engagement from a traditional penetration test. We then move onto the technical (fingers on keyboard) content as the course delves into the basics of Command & Control (C2) and uses the infamous Cobalt Strike to do so.
A major differences maker for this course in comparison to other red teaming courses is that the accompanying lab environment provides you with your own instance of Cobalt Strike to use. This is an industry leading C2 framework which has all the bells and whistles you could want. Giving students access to play with it in a lab environment is an awesome feat Zero-Point Security has managed to achieve.
Once the student has their basic footing of Cobalt Strike, much of the remaining course content focuses on covering the attack life cycle from an offensive point-of-view (the attack life cycle is the basic path a typical cyber attack follows).
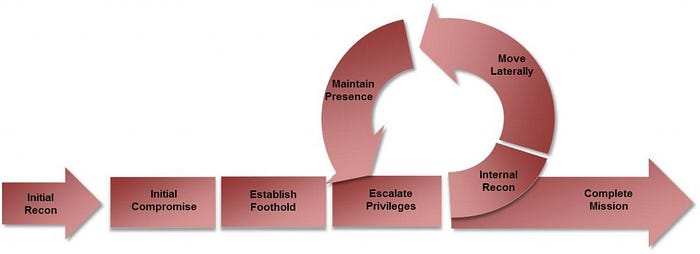
This takes you through how to initially compromise a host, perform reconnaissance, escalate your privileges, and jump to other machines on the internal network. One could equate many of these activities to an internal penetration test, though the course consistently discusses operation security (OPSEC) concerns and potential ways your activity may be caught by defenders. This focus on remaining undetected in the logs, as well as evading common Windows security…
